iPhone Hacking Toolkit Used by Russian Spies Likely Linked to U.S. Military Contractor
A powerful iPhone hacking toolkit once locked away in government cyber labs is now surfacing in global espionage and crime. In early March 2026, researchers revealed that a toolkit called “Coruna”, believed to contain 23 iOS exploits, was used not just by Russian spy groups but also by Chinese cybercriminals.
What makes this discovery chilling is the possible origin of Coruna: tools likely developed for U.S. government use by a military contractor. Instead of staying inside secure intelligence networks, this cyber‑weapon may have leaked into hostile hands. The implications are huge for iPhone security, national defense, and everyday users around the world.
Advertisement
What is the Coruna iPhone Exploit Toolkit?
The Coruna iPhone exploit toolkit is a powerful and sophisticated set of hacking tools designed to break into Apple iPhones running older versions of iOS. It was revealed by Google’s Threat Intelligence Group in early March 2026. The toolkit uses 23 distinct exploits spread across five complete exploit chains. These weaknesses target deep layers in Apple’s operating system to bypass security measures silently.
Coruna is unusual because it can compromise devices just by having a user visit a corrupted webpage. The framework fingerprints the device and picks an exploit that matches the model and iOS version. This capability lets attackers install malware without user interaction.
This exploit kit affects iPhones running iOS 13.0 through 17.2.1 but is ineffective against later and updated versions, such as iOS 17.3 and above.
How Did Coruna First Appear and Evolve?
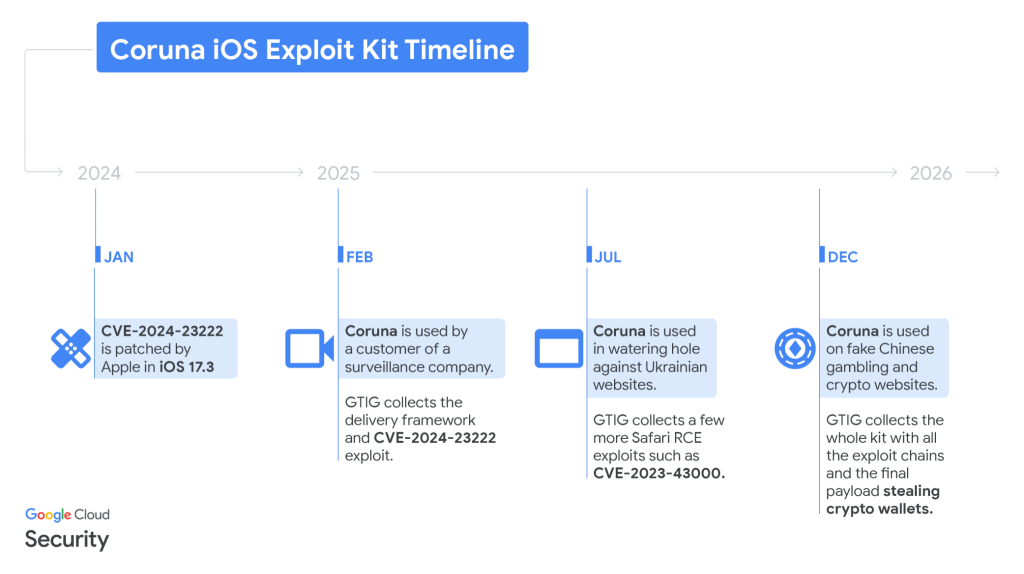
Google first observed fragments of the Coruna toolkit in February 2025 within an exploit chain used by a surveillance vendor’s customer. It was embedded in malicious JavaScript that delivered the exploit when a victim visited a compromised site.
Later in the summer of 2025, Google detected the toolkit on compromised Ukrainian sites. A threat actor tracked as UNC6353, believed to be linked to Russian espionage, deployed Coruna to target specific iPhone users in certain regions.
By December 2025, the same exploit kit surfaced on fake Chinese financial and cryptocurrency sites. Here, cybercriminals leveraged Coruna to steal funds and wallet data. This shift marked a transition from targeted espionage to broad criminal use.
Why Do Researchers Think It May Have U.S. Government Origins?
Clues from security analysts suggest Coruna may have originated in a government‑linked development environment. The toolkit’s technical depth and quality indicate significant resources behind it, often associated with state‑level intelligence tools.
A key factor is the English‑language documentation and coding style in the exploits, which researchers note is typical of tools developed for Western or U.S. clients. Some analysts, including those at iVerify, believe components of Coruna share similarities with exploit modules used in earlier espionage campaigns like Operation Triangulation.
However, cybersecurity firm Kaspersky disputes direct code reuse evidence, cautioning that high complexity alone does not confirm a U.S. government or NSA connection. Researchers are still analyzing the origins.
Who Has Used Coruna and for What?
Russian Espionage Operations
In mid‑2025, a suspected Russian state‑linked group known as UNC6353 used Coruna in “watering hole” attacks. These attacks embed malicious code in compromised Ukrainian websites. When iPhone users visited these sites, the framework silently targeted their devices.
Chinese Cybercriminal Campaigns
Later, the same toolkit appeared on fake Chinese gambling, finance, and crypto platforms used by a financially motivated group tracked as UNC6691. They aimed to steal cryptocurrency and financial data from victims.
Broader Impacts
Because Coruna relies on older vulnerabilities, its use shows how zero‑day and second‑hand exploits can circulate between state actors and criminal networks, creating widespread risk.
How Does Coruna Exploit iPhone Security?
Coruna uses multiple advanced techniques to compromise iPhones:
- WebKit Remote Code Execution (RCE): Allows browser‑based entry points to execute malware.
- Pointer Authentication Code (PAC) Bypass: Evades security features designed to prevent memory corruption.
- Kernel Escalation: Gains high‑level system privileges.
- Sandbox Escape: Breaks out of app restrictions to access wider phone data.
The exploit chains leverage known vulnerabilities in iOS 13 to 17.2.1. Most of these vulnerabilities have since been patched by Apple, reducing the risk for updated devices.
What Has the U.S. Responded To These Threats?
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added several vulnerabilities exploited by Coruna to its Known Exploited Vulnerabilities (KEV) catalog in March 2026. This listing pushes federal and private entities to patch the bugs quickly.
At the same time, the U.S. Treasury has sanctioned a Russian zero‑day broker accused of dealing in stolen exploits tied to these tools. Those sanctions aim to disrupt the trade in advanced hacking tools.
Which iPhones are most at Risk?
Coruna affects phones running older iOS versions, including:
- iOS 13.0 (released 2019)
- iOS 14, 15, 16
- iOS 17 up to 17.2.1 (released Dec 2023)
Devices with iOS 17.3 and newer are not vulnerable to this toolkit. It is essential to stay updated to the latest iOS version and enable optional protections like Apple Lockdown Mode, which adds extra defenses against exploit kits and targeted attacks.
How iPhone Users Can Protect Themselves?
Updating your device remains the top defense. Install the latest iOS version as soon as Apple offers it because patching removes exploited vulnerabilities. Beyond updates:
- Enable Lockdown Mode for higher security.
- Avoid suspicious websites and online ads.
- Do not visit unknown links, especially on older devices.
These steps help block exploit kits like Coruna and protect data and financial accounts.
Final Words: What Does This Mean for Mobile Security?
The journey of the Coruna exploit toolkit, from possible government roots to wide misuse, underlines how critical it is to defend mobile devices against modern threats. The case also shows how powerful tools designed for intelligence can leak into criminal hands.
With cybercrime and nation‑state hacking on the rise, individuals and organizations must update regularly and stay alert. Using an AI security analysis tool to monitor threat indicators can also help detect unusual activity before major damage occurs.
Advertisement
Frequently Asked Questions (FAQs)
The Coruna toolkit uses iOS flaws to access iPhones silently. It was reported to be active in March 2026.
Fully updated iPhones are mostly safe. Coruna exploits older iOS versions. Always install updates. Reported March 2026.
Experts suspect Coruna may have originated from a U.S. defense contractor. No official confirmation yet. Information reported March 2026.
Disclaimer:
The content shared by Meyka AI PTY LTD is solely for research and informational purposes. Meyka is not a financial advisory service, and the information provided should not be considered investment or trading advice.
Advertisement
What brings you to Meyka?
Pick what interests you most and we will get you started.
I'm here to read news
Find more articles like this one
I'm here to research stocks
Ask our AI about any stock
I'm here to track my Portfolio
Get daily updates and alerts (coming March 2026)